Every quarter, we publish compliance and security insights that you can share with your employees to fulfill periodic security reminder requirements your organization may be subject to.
As an added bonus, we’ve highlighted some developing security trends and featured a quick tip to get more out of your compliance management.
Reduce Compliance Management to Bite-size Chunks
Whether you’ve been doing compliance for a decade or you’re brand new to the game, you’ve probably been approaching compliance management as a once-a-year event. We tend to treat it like “Compliance Season” — kind of like Deer Season or Duck Season. Suddenly, everyone goes into “Compliance Mode,” we do compliance activities for a frantic period of time (typically lasting months), and then everyone goes back to normal work for the rest of the year until it’s time to start the annual scramble all over again.
The purpose of a security and compliance program is to protect the organization, and that’s not something that happens once a year. It requires tasks that need to be done every day, every week, every month, every quarter, twice a year, and annually. These periodic tasks form the controls that assist in the active protection of your company. If you only touch them once a year, you aren’t running a program, you’re just surviving an audit.
To fix this, migrate your compliance program into what TCT calls “Operational Compliance Mode.” This is where you take those mountainous tasks and spread them out across the course of the year. By shifting to this continuous rhythm, you move away from the tyranny of the urgent and make compliance something you maintain in small, manageable chunks.
This single change will be transformative for your compliance program. You’ll run smoothly and you’ll gain more control. No more enduring a disruptive, haphazard annual event that throws grit in the gears of your daily operations.
Automate the Rhythm of Your Compliance Program
Migrating to Operational Mode doesn’t have to be overwhelming. By leveraging a compliance management system like TCT Portal, you can effectively automate the coordination of Operational Mode so it runs in the background, without needing your continual attention.
Typically, organizations set Operational Mode to a quarterly cadence. If you’re on an annual cycle from January to December, your Q1 tasks will start coming due around the end of March. You queue up the periodic and circumstance-based evidence — like quarterly vulnerability scans or incident response documentation — assign the right people, and instruct the system to ping them when it’s time to load evidence.
This gives you oversight without the manual scramble.
Speed up Onboarding (and be Organized for Audits)
One of the biggest risks in a haphazard compliance program is personnel turnover. Bob has been doing the work for six years. Bob leaves, and Mary steps in. But Bob didn’t tell Mary everything she needed to do.
In the annual scramble model, you won’t discover that gap until you’re sitting in your annual assessment with the Assessor. Suddenly you’re blindsided when the Assessor asks you for Mary’s evidence and you can’t produce it. That’s when everyone starts sweating bullets, asking, “What do we do now?”
When you manage compliance in Operational Mode, you have a far better capability to catch these issues sooner. Because everything is documented within TCT Portal, you have near-term insight into whether or not the team is on track.
Even if Bob didn’t train Mary properly, Mary can log into TCT Portal and see exactly what Bob did in previous years, when he did it, and what evidence the Assessor approved. She can get up to speed efficiently and expediently, and you have a system that gives you an eye on the controls to protect the organization overall.
Level up the Assessor Relationship
The relationship with your Assessor will benefit from making the shift to Operational Mode. Assessors love it when an organization has detection mechanisms in place, because they see that you’re discovering issues, addressing them, and correcting them in real time. It signals that you’re taking compliance seriously and have your act together.
And that trust makes annual assessments go much easier.
Ease the Burden of Annual Tasks
Take Operational Mode to the next level by spreading out those heavy one-time annual tasks throughout the year. Even if you do the quarterly elements, you could still be left with a massive amount of stuff due at the end of the year.
Talk to your Assessor to determine what pieces of evidence are best to collect earlier in the compliance cycle. For example, you might create a compliance calendar that looks something like this:
- Q1: Conduct all annual policy reviews
- Q2: Handle all security awareness and training activities
- Et cetera
Spreading these tasks out dramatically lowers the stress level for everyone involved.
Lower Stress, Less Overwhelming, More Productivity
If you take that annual glut of compliance activities and sprinkle it across the year, your organization avoids overwhelming your personnel and diverting them for months at a time from their essential tasks. Instead, the team can spend a predictable amount of time every week on compliance, and no one is overloaded.
Need help transitioning to Operational Mode? Contact TCT and we’ll help you make the move to greater compliance sanity.
TCT Portal Quick Tip: EZ Cert Is the Compliance Interface for Non-techies
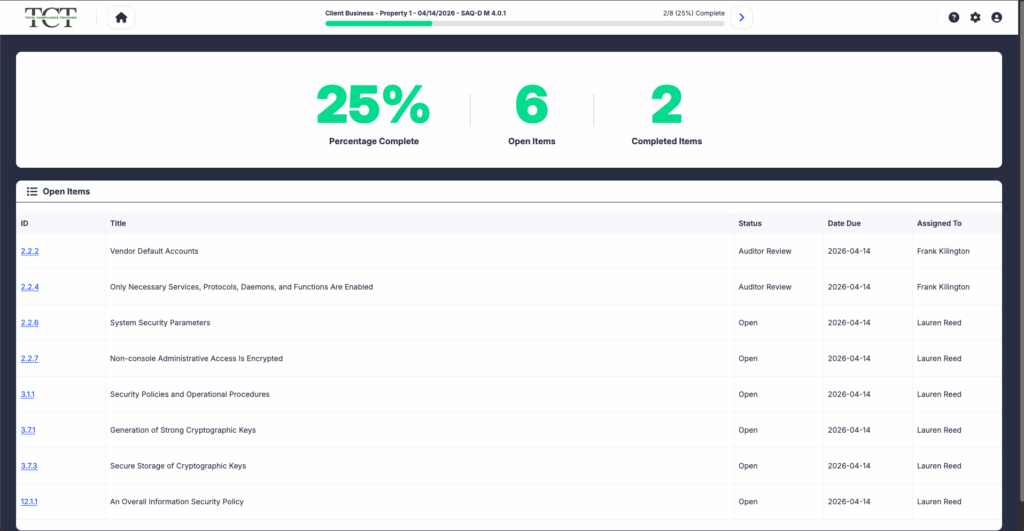
For the person who lives in compliance every day, TCT Portal is a powerhouse. It has an astounding amount of capability, and for power users, that’s exactly what they need to manage a complex engagement.
But there’s also the periodic user. Maybe it’s someone in HR, a non-technical manager, or even a technical lead who only needs to step into the platform once a year. To them, entering a full-featured compliance management system can feel like sitting in the cockpit of a fighter jet when all they wanted to do was drive to the grocery store.
They don’t want the complexity — they want to get their work done and get back to their “real” job.
That’s why we introduced EZ Cert.
EZ Cert is a simplified, streamlined interface designed specifically for control owners who only need to see what they’re responsible for. EZ Cert removes the administrative noise and lets them focus on their specific tasks.
When a user logs in via EZ Cert, they get an active dashboard that gives them total clarity:
- What do I have? They see only their assigned items.
- How far along am I? A clear progress bar shows exactly what percentage of the work is complete.
- What do I do next? The interface directs them to the evidence they need to provision for the engagement.
You Control the Complexity
One of the best things about EZ Cert is that it isn’t an all-or-nothing interface. As a compliance manager, you can configure it at the individual user level, so each user sees just what they need to see.
A Professional Client Experience
If you’re a Consultant or an Assessor, EZ Cert is a game-changer for new client engagements.
When you onboard a brand-new client, you can start them on the EZ Cert interface from day one. They haven’t seen the full Portal yet, so their first impression is a clean, focused, and intuitive experience. It makes the engagement feel manageable rather than mountainous, allowing them to focus on their requirements instead of trying to figure out the complexity of the software.
Make Compliance Management Suck Less
At the end of the day, compliance is about protection, but it’s also about personnel. By stripping away the busywork and the interface slog, you make compliance management suck less for everyone involved.
EZ Cert is currently available to all TCT Portal customers. Learn more about EZ Cert, or contact Portal Support to discuss deploying it at your organization.
What’s Going on in Security Today
Under Armour ransomware breach: data of 72 million customers appears on the dark web
Under Armour suffered a ransomware breach that was reported in January 2026. The attack involved the exposure of a massive customer dataset on the dark web following a November 2025 attack by the Everest ransomware group. The leaked database reportedly contains over 191 million records, including approximately 72 million unique email addresses, as well as full names, phone numbers, geographic locations, genders, and detailed purchase histories.
While Under Armour’s official communications were initially cautious, the Everest group published the data after the company allegedly missed a ransom deadline. This incident highlights the “double-extortion” tactic where attackers not only encrypt systems but also exfiltrate and leak sensitive data to pressure victims, often leading to secondary risks like targeted phishing and identity theft.
Conduent data breach among the largest in U.S. history
Conduent experienced one of the largest data breaches in U.S. history from October 2024 through January 2025. The breach involved the theft of sensitive healthcare and personal data belonging to at least 25 million individuals. Conduent’s compromise exposed Social Security numbers and regulated health information, leading to massive regulatory scrutiny and class-action lawsuits.
The breach is particularly notable for its delayed notification timeline — while disclosures to regulators began in early 2025, affected individuals were not directly notified until October of that year. This delay exacerbated the risk of long-term harm, such as medical identity theft and financial fraud, which can haunt victims for years after their data appears on underground marketplaces.
Critics call FCC router rule a ‘big swing’ that could create more supply chain uncertainty
The FCC is moving to ban foreign-made routers in the US. This has been a vaguely rolled out Announcement, and it’s causing an immediate slowdown or halt in router and Wi-Fi device sales for foreign companies such as TP-link. Meanwhile, router and Wi-Fi device manufacturers in the United States, such as Netgear or Starlink, have seen jumps in sales already, mere days into the announcement.
Axios npm package compromised to deploy malware
Following an apparent takeover of a legitimate maintainer account, updates were made to a couple of versions of Axios. Axios is a widely used JavaScript HTTP client for web and Node.js applications.
The scary part about this particular attack vector is that an attacker published unauthorized package updates that appeared legitimate, making organizations unable to tell they were loading nefarious updates to these packages.
If your organization uses Axios, make sure to validate the versions you have installed and update them ASAP.
SIM Swaps Expose a Critical Flaw in Identity Security
There’s a new type of physical attack that makes the “trusted phone number” anchor in security a misplaced mindset. The attack is called a SIM swap attack.
The cyber criminal essentially gets a mobile carrier rep to transfer a victim’s phone number to a new SIM card that’s in the attacker’s possession. Once reassigned, the attacker can take the identity of the mobile device, intercepting OTPs and MFA prompts. They can initiate password resets, token resets for banking apps, and more.
Iran Built a Vast Camera Network to Control Dissent. Israel Turned It Into a Targeting Tool
Iran has a network of hundreds of millions of cameras throughout their country, on shops, in homes, street corners, among other places. The country’s government had been warned that their cameras had been compromised, but officials didn’t heed the warning. This ultimately was determined to be the reason their Ayatollah was taken out.
The irony for authoritarian countries is that the systems they put in place to squash dissent, if compromised, were turned into a tremendous detriment. One security engineer from California figured out he could hack millions of cameras globally without leaving his home.
Get industry insider expertise delivered to your inbox
Subscribe to the TCT blog